Businesses requirement to manage clients
proficiently and viably calls for a steady change in their telephone
framework. What’s more, they have to minimise issues, for example,
unauthorised utilization of telephone services and toll fraud (Phone
Hacking). One of the real tests is to screen the uncalled for
utilization of corporate correspondence offices for toll calls. The
abuse of authorisation codes is a significant concern for different
sorts of businesses. Toll fraud can happen with TDM and IP-based voice
frameworks. From representatives that try to make a couple of free calls
to programmers, any telephone framework could be helpless.
Notwithstanding, call logging programming can dispose of this issue by
guaranteeing that a phone framework is not traded off. Call logging
includes catching call records, archiving them in a database, and after
that recovering them by method of a reporting interface.
Call logging programming can track toll
misrepresentation and give cautions and reports of abnormal phone
action. The programming enactss as a framework watchdog for VoIP
requisitions, cautioning overseers of any suspicious calling movement.
This incorporates calls to global ends of the line, visit lines,
stimulation services, grown-up services, and that’s just the beginning.
In the period of terrorism, it is paramount for calls to be followed.
Reports prepared by call logging
programming might be utilized to build business effectiveness with extra
mixed programming modules. Phone call information might be gathered and
broke down for different purposes incorporating the overseeing of
expenses. By taking a gander at these records, a business can figure out
toll duplicity as well as screen the expense of calls and make
important move to lessen such takes. It is likewise conceivable to
figure out the amount of unused or abused developments in a system.
Call logging programming likewise
empowers businesses to enhance the execution of workers by examining how
rapidly they address inbound calls. The information could be utilized
to prepare and order staff to end up additional profitable. With
security being a real concern, it is critical to pick the right
telephony framework, for example, Cisco Phones and Mitel Phones that
offer call logging characteristics to help avoid dangers, for example,
toll cheating. Cisco IP Phone s emphasize the bound together
interchanges framework that gives clients a protected correspondences
system.
Counteractive Action is Superior to Cure:
So what pragmatic measures can telecom or IT administrators take to help anticipate being an alternate casualty of wrongdoing?
A standout amongst the best methodologies
to enhancing the security of telephony frameworks incorporates leading
customary reviews of:
- Station benefits and confinements
- Voice and information calling examples
- Public and private system steering access
- Automatic way determination
- Software characterized systems
- Private exchanged and pair systems
Different measures incorporate evaluating
the design of your PBX in the light of known programmer methods and
looking at arrangement portions against best practice and any
administrative prerequisites that may relate to your industry area.
Guarantee default voicemail and support
passwords are changed and acquaint an arrangement with anticipate
effectively guessable passwords being utilized.
Verify that the arrangement requests consistent watchword changes and make moves to guarantee the approach is authorized.
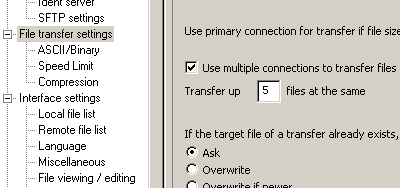
Introducing a call logging result, to
furnish notice of suspicious action on your PBX, is a convenient measure
and one that can frequently bear the cost of profitable unanticipated
cautioning of a strike. Audit existing PBX control works that could be
at danger or which could permit slips to happen, as well.
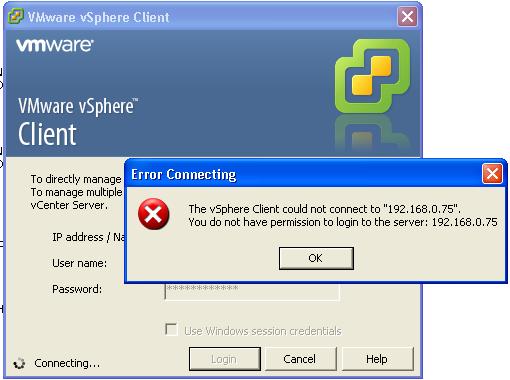
Be conscious that numerous voice
frameworks now have an IP address and are in this way associated with
your information system – evaluate what procurements you need to section
both systems. Security exposures can likewise come about because of the
way various PBX stages are joined over a corporate system or from
interconnectivity with existing provisions.
Research and examine working framework
shortcomings – incorporating explanatory discoveries, make suggestions,
prioritisation and alleviation or conclusion needs – and execute a
standard calendar of exploring server administration packs, patches,
hot-fixes and against infection programming.
Call logging programming is utilized by
numerous businesses over the globe to screen and oversee phone calls,
cut expenses, and increment bargains and benefit. In this way, little
and medium ventures with a fundamentally high calling action should
think about putting resources into call logging software.
Good phone systems are very useful when
doing business in any company. The managers, employees, owners of the
businesses, suppliers and the consumers of the company goods and
services use phone systems
to communicate to each other making the process of goods and services
easy to produce and offer to their clients. Clients will ask questions
and give their feedback through the phone. This makes the service
delivery more professional and many client will prefer a company with a
good phone framework and this will increase the profits in the business.








 Getting hacked sucks, plain and simple. It can affect your rankings, cause your readership to be exposed to virus and trojan attacks, make you an unwilling promoter to subject material you may not actually endorse, and in many cases cause the loss of valuable content. However, once it happens it is usually best to not procrastinate on the clean up process, since a speedy restore will most times minimize the damage that was caused.
Getting hacked sucks, plain and simple. It can affect your rankings, cause your readership to be exposed to virus and trojan attacks, make you an unwilling promoter to subject material you may not actually endorse, and in many cases cause the loss of valuable content. However, once it happens it is usually best to not procrastinate on the clean up process, since a speedy restore will most times minimize the damage that was caused.